10 Hottest Tech Companies 2021

Over the past few decades, the internet has been enthusiastically embraced by millions of businesses. People too find it comfortable to have everything on the internet. The web provides the best way for marketers to get to know the people visiting their sites and start communicating with them. As the number of businesses over the web increases, so has the use of web applications and cloud services increased. Web applications raise several security concerns despite the advantages due to loopholes in code or lesser security standards. These vulnerabilities are often abused by attackers who want to gain access to sensitive company data or even users' private data.
Axis Security enables any organization to quickly deliver tightly managed global access to employees, partners, and other stakeholders through a purpose-built zero-trust cloud security platform. Unlike legacy solutions that create excess access and unnecessary risk, Axis Security's unique Application Isolation Technology assures access to only required resources. The company sees a world where access to business applications is fully managed and secured based on modern architecture, innovative technology, and a zero-trust business-centric approach. Its technologies aim to transform open networks and vulnerable applications into fully protected resources that the business can leverage and trust to grow in a myriad of ways.
Application Access Cloud
The Application Access Cloud lets you protect your business with a solution that's faster to deploy, simpler to manage, and more secure than you ever thought possible. You can quickly empower end-users (employees and 3rd parties) with easy-to-use, instant access to apps and resources and leverage the flexibility of a cloud solution for access that can automatically scale with your enterprise. The application also reduces the amount of time and effort you spend on administration by taking advantage of centralized management. You can easily connect end-users, even with unmanaged or 3rd party owned devices, to any app or resource wherever they are located. It helps you deliver secure access without endpoint agents or reconfiguring your network. Some of the significant benefits include:
Accelerate Your Business: You can connect employees to resources immediately through an amazingly fast and straightforward deployment without changing your network.
Easily Connect Users to Apps: Employees get more work done with easy-to-use secure access to apps and resources, even with BYOD.
Protect & See Everything: Continuous visibility over user behavior with zero trust policies to control access permissions down to the finest detail.
Enterprise Scale & Integrations: Global cloud service scales with demand and integrates with existing security to power adaptive policies and automate management.
Simple Access to Sophisticated Technology
Today's work doesn't just happen inside the office – it's all over the world. Business applications are forced to tunnel each user through VPNs and proxies that are painfully hard to set up, frustrating to use, and constantly break. There can be a highly sensitive attack surface in the process. With Application Access Cloud, private application access is finally simple. Users connect directly to apps via one central hub without touching the network or the apps themselves. No more VPN tunnels or agents are needed. No lengthy deployments or complex configurations. No network attack surface to worry about. Just safer, simpler app access for all your users.
Completely Isolated From Your Network: Mediates access between users and applications without granting excessive access to your network or the applications themselves.
Driven By User Behavior Intelligence: Analyzes how users interact with your applications to detect anomalies and flag potential problems.
Secure Through Continuous Authorization: Uses a zero-trust approach to constantly verify and change permissions, ensuring users only have access to what they need.
The importance of Third Party Access
Successful enterprises prosper through collaboration with partners, contractors, and other third parties who are not formal employees. These partner stakeholders need access to critical business applications and resources located on-prem or in the cloud. But allowing them onto corporate networks to access vulnerable applications via VPN or using VDI is too risky, expensive, and complex. And you probably don't manage their devices, so anything that requires an agent is right out.
Axis Application Access Cloud instantly, simply, and safely extends application access to partners and third parties securely enabling them anywhere. It protects the enterprise by enforcing granular controls over user access permissions and isolating applications from users, networks, and the internet while brokering and sanitizing user requests. Deployment is lightning fast with no network changes, agentless, and a central cloud console manages it all easily through centralized policies.
Mergers & Acquisitions
The easy, low-risk way to extend secure application access to users across separate organizations without IT exposure or consolidation. Acquisitions are the fastest way for businesses to win. Reducing risk and consolidating operations before and after a merger is critical to ensuring success. Any delay in getting stakeholders in one organization access to resources in the other directly impacts the bottom line. Yet, newly acquired networks may be compromised. Maintaining separate networks and multiple VPNs can prevent users from accessing critical resources, but technology integrations can take years.
Axis Security's Application Access Cloud instantly and simply enables low-risk zero trust access to applications and resources across organizations without merging networks. Its highly scalable service brokers easy-to-use agentless access to resources located anywhere while isolating them from potentially compromised users, devices, and networks. Deployment is lightning fast with no network changes, and a central cloud console manages it all easily through cross-application policies.
Secure Access for Cloud Migrations
Migrating apps to or between clouds is complicated. Reconfiguring your VPN and network to access a newly relocated application can be complicated and disruptive to users. It also means accepting ongoing management complexity and infrastructure traffic better offloaded to the public internet. Axis Application Access Cloud is a scalable enterprise-grade service that lightens the load on your existing network resources. With Axis, you can reduce the risk of disrupting user access to critical resources and avoid reconfiguring your infrastructure by using the same centrally managed access solution and policies before and after migration. Axis also improves your security by isolating your apps and sensitive resources from users, networks, and the internet.
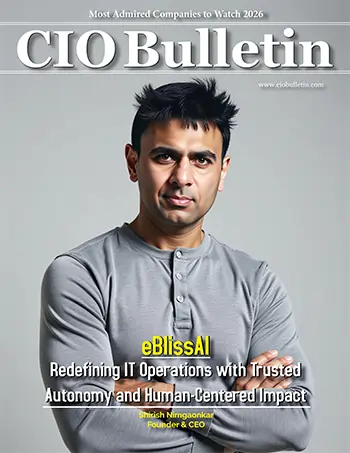
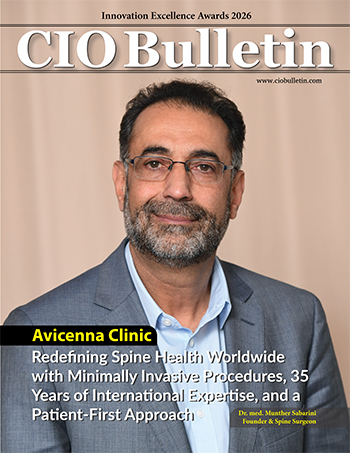
Meet the CEO
Dor Knafo is CEO and Co-Founder of Axis Security. Before co-founding Axis Security, Dor has served as a senior security researcher at Fireglass, a leader in web isolation, and later acquired at Symantec. Dor is a five-year veteran of the elite Unit 8200 of the Israeli Army Intelligence Corps as a senior software engineer for advanced cybersecurity. He has a Bachelor of Science degree in Computer Science from IDC Herzliya.